
DELEGATE THE MANAGEMENT OF YOUR CYBER COMPLIANCE
Compliance is not negotiable. Our mission is to take 100% ownership of the management of your Information Security.
The Context: Complexity and Constraints of Cyber Compliance
Increasingly Complex Obligations
- • European (NIS2, DORA, GDPR, etc.) and national laws (ANSSI).
- • Hundreds of technical, organisational and legal requirements.
- • Technical migrations to anticipate (e.g. Post-Quantum Cryptography – PQC).
Compliance Is Not Negotiable
- • Cyber certifications (ISO27x for example) are mandatory in many sectors.
- • Continuous activity, requiring permanent monitoring and controls.
- • Known and significant sanctions and penalties in case of non-compliance.
Limited Resources and Conflicting Priorities
- • Lack of time to dedicate to Information Security management.
- • Difficulty recruiting skilled resources on such complex topics.
- • Budget constraints in an uncertain economic environment.
Our Commitment to Cyber Compliance
TAKING 100% OWNERSHIP
Of the cyber compliance management of our clients
Executives & Decision-Makers
Gain a consolidated view of your cyber practices against your obligations.
Compliance Teams & CISOs
Delegate all or part of the tasks with full confidence and save time delivering the expected evidence.
Technical Contributors
Benefit from recognised technical and PQC expertise for cryptographic migrations.
A Unique Approach: Better than a Dedicated Employee
Flat-Fee Model
Cost control & commitment to results.
Operational Delegation
Continuous compliance & single point of contact.
Constant Reassurance
Accessible web service & real-time alerts.
State-of-the-Art
Service always up to date, managed by experts.
REGnance Services: Full Coverage of Your Compliance Lifecycle
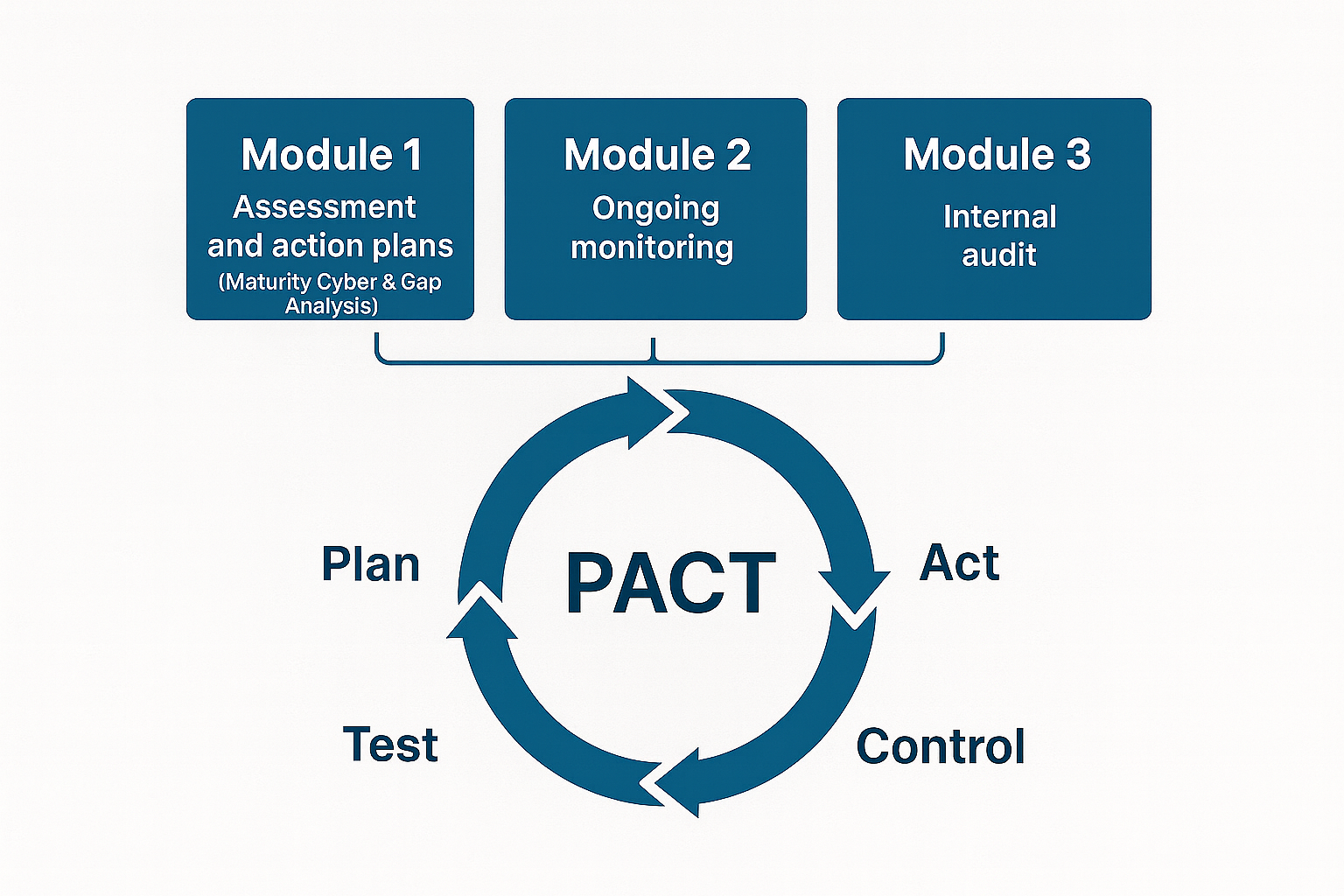
DIAGNOSTIC
One-Off
Review existing documentation, identify regulatory, organisational and technical gaps, and build the roadmap.
- Initial findings report
- Concrete recommendations
- Compliance action plan
ONGOING MONITORING
Recurring (Update, Control, Steer, Test)
A cycle of governance tasks, organised by topic, to steer cyber practices continuously (reporting, dashboards).
- Policies, procedures and other documents kept up to date
- Risk mapping regularly reassessed
- Cyber dashboards for top management
VERIFICATION
One-Off (Internal Audit)
Assess the level of security: check that measures are implemented, review evidence, and identify gaps and priority weaknesses.
- Internal audit report
- Remediation plan follow-up
- Summary of DRP/BCP/Cyber crisis exercises
Post-quantum cryptography (PQC) practice
REGnance offers specific expertise in anticipating the quantum threat. In partnership with industry technology leaders, we support you during the discovery phase to inventory your cryptographic assets and during the remediation phase to implement cryptographic agility.
Our Expertise: People, Tools, Values
Multidisciplinary Experts
- ➜ 15+ years of dedicated experience per compliance lead.
- ➜ Governance, technical and legal expertise.
- ➜ Technical mastery: participation in standardisation committees / recognised PQC expertise.
Know-How and Values:
- Operational excellence
- Transparency, integrity and independence
- Multi-client experience (operational assurance)
Dedicated Tools
A web platform shared with the client for unified and sovereign management (hosted in France).
- ➜ Unified: replaces your multiple tracking files.
- ➜ Intuitive & AI-native.
- ➜ Key features: risk tracking, audit steering, remediation actions, incident management.
- ➜ Information security documentation framework & continuous monitoring.
References & Experience
- ➜ Several hundred consulting engagements delivered.
- ➜ 30+ compliance audits per year.
- ➜ Dozens of certifications/qualifications obtained or maintained.
- ➜ All sectors, both public and private.
Ready to delegate your compliance?
Get in touch for an initial discussion and let’s build your roadmap together.
contact@regnance.comFAQ – Cyber Compliance & REGnance Support
What is cyber compliance for a company? ▼
Cyber compliance means aligning your information security practices with laws, regulations and frameworks (NIS2, DORA, GDPR, etc.) in order to control your risks and avoid sanctions or major incidents.
How does REGnance help me comply with NIS2, DORA and GDPR? ▼
We perform a diagnostic of your practices, build a compliance roadmap, update your information security documentation framework and run ongoing monitoring to track your obligations over time.
What is the difference between a one-off audit and ongoing monitoring? ▼
Ongoing monitoring tracks your risks, actions and documents on a continuous basis. A one-off audit checks, at a given point in time, that measures are applied, evidence is available and highlights gaps and remediation priorities.
Who is REGnance’s offer designed for? ▼
We primarily support SMEs, mid-caps and organisations subject to strong cybersecurity requirements (sector regulations, certifications, supervision by authorities or regulators).
How does a typical engagement with REGnance work? ▼
We start with a diagnostic and an inventory of your practices, define priorities with management, implement governance processes and tools, then provide regular follow-up through our platform and steering committees.